Security Roles and Permissions allow system administrators to create a standard grouping of permissions that can be assigned to users, and these roles determine what individual users can access and do within the system. Security roles are important because they enable an organization to grant certain people access to certain data and also restrict access to certain data.
| Managing Security Roles | Additional Information | Training and Troubleshooting Resources | ||
|
The Permissions page displays the permissions that are in the role.
To create a security role, go to . Then, click the Create New Role link.
| PERMISSION NAME | PERMISSION DESCRIPTION | CATEGORY |
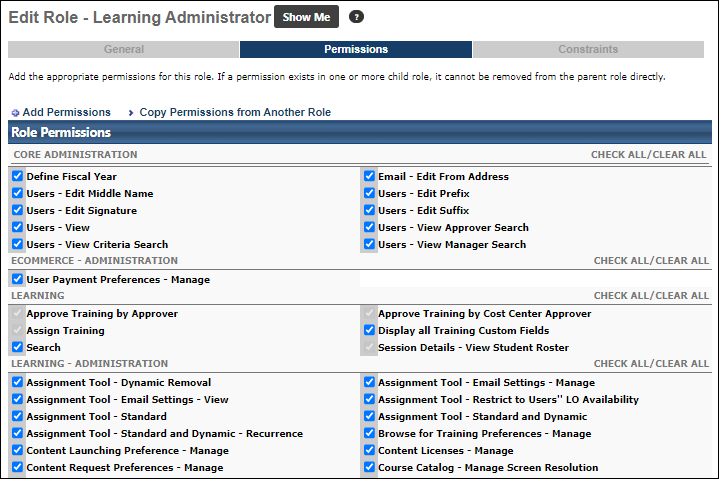
This section allows you to add permissions or copy permissions from another role. An administrator can only add permissions to a role using permissions available to them. The system will check, based on your access, what roles you can create based on your individual permissions and constraints.
- Select either Add Permissions or Copy Permissions from Another Role link:
- To copy permissions, search for role and click Add icon.
- To add permissions, search for permission and check the add box and click .
- Search for available permissions by name in the select field or by category.
- Click the button to select or deselect permissions.
- Click the Add box next to each permission.
- Click . The selected permissions will be added to this role.
- Click to continue to the Constraints section. See Security Role - Create - Step 3 - Constraints.
Helpful Hints
When editing an existing parent role that has at least one child role, you cannot deselect any permissions in the parent role that have been included in a subordinate/child role.