View Permissions Constraints Details
The Permissions Constraints Details page provides administrators with an investigative tool to review and analyze a user’s security profile. For example, if a user reports that they cannot access a page that was previously available to them, this page provide administrators with pertinent information to help streamline the analysis. Having this information on demand allows administrators to take prompt and corrective action more efficiently.
See How to Use Permissions Constraints Details.
To access the Permissions Constraints Details page for a user, go to . Select the Options drop-down for the user and select the Permissions Constraints Details option.
| PERMISSION NAME | PERMISSION DESCRIPTION | CATEGORY |
| User Permission and Constraint Details - View | Grants ability to access the Permissions Constraints Details page for a user. This permission also grants ability to see the Permissions Constraints Details link on the Permissions page. This permission can be constrained by OU, User's OU, User, and User Self and Subordinates. This is an administrator permission. | Core Administration |
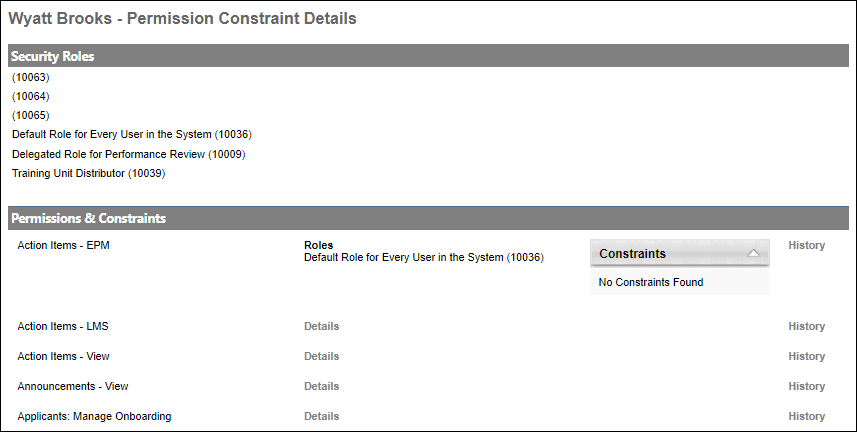
Security Roles
The Security Roles section displays each of the security roles to which the user is assigned. This includes custom security roles assigned to the user and system-defined security roles that are dynamically assigned to the user, such as Manager and Default Role for Every User in the System.
This section displays the security role title and its corresponding role ID.
Permissions & Constraints
The Permissions & Constraints section displays each of the user's permissions and their corresponding roles, constraints, and audit history.
View Permission Details
Select the Details link next to a permission to view each of the user's security roles that contain the permission and any constraints applied to the permission.
View Permission History
Select the History link next to a permission to view history information for the permission.
Note the following:
- All dates and times are displayed in AM/PM format and are localized to the logged in user's time zone.
- No historical data is available to system defined roles, such as Manager, Approver, and Default Role for Every User in the System.
The following information is displayed:
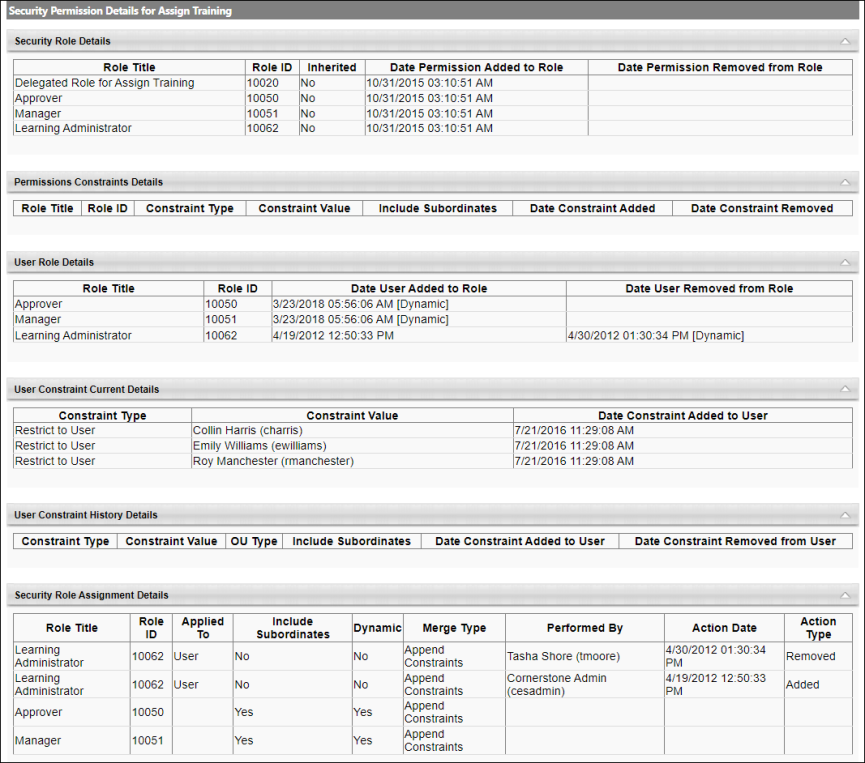
- Security Role Details - This section displays details about the user's current and historical security roles that contain the permission. The security roles displayed are based on the user's history with the permission. For example, if the permission is associated with ten security roles in the system but the user is only associated with two of these security roles, then only the two security roles associated with the user are displayed in this section.
- Permissions Constraints Details - This section displays historical details of the constraints that have been defined for the permission at the role level. This section displays the type, value, and dates when the constraint was added or removed.
- User Role Details - This section displays when the user has been added or removed from the security role that contains the permission.
- User Constraint Current Details - This section displays the user's current constraints applied to the permission. The constraints reflect only what the user currently has from roles already assigned as well as system roles, such as Manager, Approver, and Default Role for Every User in the System. Constraints from dynamic roles not yet assigned to the user are not reflected in the list.
- User Constraint History Details - When available, this section displays the user's current and previous constraints applied to the permission.
- User constraints auditing data are currently not captured in Production and Pilot environments. This will be enabled in Q3. User constraint historical data will only be available from the point auditing is enabled. That is, no user constraint actions (add or remove) that occurred prior to auditing being enabled will be captured in this table.
- Security Role Assignment Details - This section displays details of the historical assignment of the security roles that contain the permission. The details include the following information:
- Users or OUs to whom the role was assigned or removed, including subordinates
- Whether the action was immediate or dynamic
- The merge type for the constraints
- The administrator who performed the action
- The date and time of the action
Note: Although administrators cannot perform assignment actions on system-defined roles, these records are still included in the table for visibility purposes.