Security Role - User Permission Report
The Security Role - User Permission Report enables organizations to extract details on the roles assigned to a user and the permissions and constraints associated with those roles. This report also includes constraints at the individual user level. Filtering options are available.
This report supports 100,000 rows of data.
To access the Security Role - User Permission Report, go to . From the System tab, select the Security Role - User Permission Report link.
| PERMISSION NAME | PERMISSION DESCRIPTION | CATEGORY |
| Security Role - User Permission Report | Grants access to the Security Role - User Permission Report, which enables organizations to report on the roles assigned to a user and the permissions and constraints associated with those roles. This permission cannot be constrained. | Reports - System |
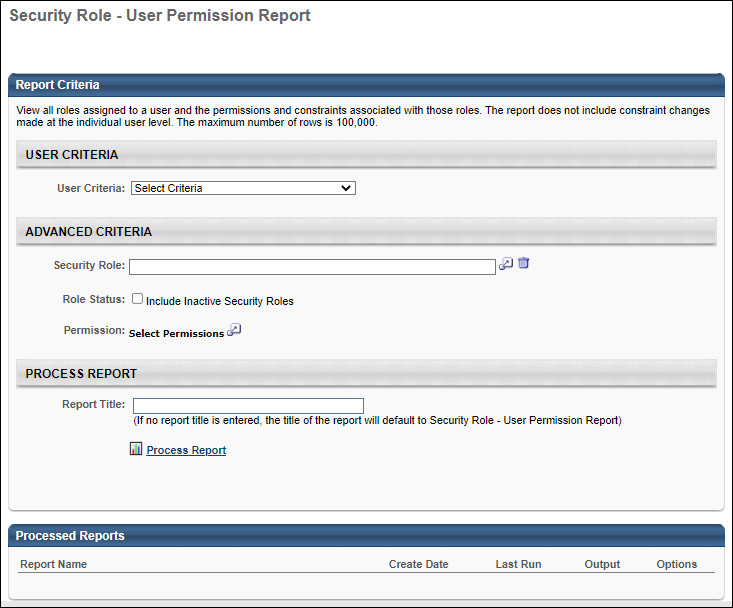
Report Criteria
The following report filters are available:
| Filter Name | Description |
|---|---|
| User Criteria | Select a user or a group of users to include in the report. You may choose one or more individual users as well as entire organizational units (OUs) or Groups. |
| Security Role |
Select a security roles to include in the report. If a role is selected, the report only includes information related to the selected role. The Security Role filter is visible to all users. However, a Restricted Access error message is displayed if an administrator attempts to use the filter or process the report if they do not have the permission. Further, administrators can only view security roles that are within their and permissions. |
| Role Status | Select whether the report should include inactive roles. |
| Permission | Select one or more permissions to include in the report. If a permission is selected, the report only includes information related to the selected permission. |
Report Output
The following details are included in the report output:
| Column Name | Description |
|---|---|
| User ID | This displays the ID of the user in the security role. |
| Username | This displays the username of the user in the security role. |
| User Full Name | This displays the full name of the user in the security role. |
| Constraint | This displays the constraint applied to the security role. |
| Security Role Name | This displays the name of the security role. |
| Security Role ID | This displays the ID of the security role. |
| Security Role Type | This displays the type associated with the security role. |
| Security Role Active | This displays whether the security role is active or inactive. |
| Parent Security Role Name | This displays the parent security role associated with the security role. |
| Parent Security Role ID | This displays the ID of the parent security role. |
| Permission | This displays the permission included in the security role. |
| Permission Category | This displays the category of the permission included in the security role. |
| Inherited Permission | This displays whether or not the permission is inherited from a child role. |
Considerations
The Security Role pop-up will show only the roles that a user is part of AND the child roles of those roles.